Russia’s special military operations in Ukraine brings to the foreground the geopolitics of data routing and the manner in which states use data routing in contested areas to assert their power
Krutika Patil
In the aftermath of the 2014 Russo-Ukrainian conflict, Russia gained control over the Crimean internet network, as well as that of the Donbas region. Through data protection laws and various other measures, Russia gradually created a Sovereign Internet/RuNet that gave it complete control of all Internet Transit Points in that region through which data packets flow in the network. Even before Russian troops set foot in Donbas in the current conflict, Russia had complete control over the region’s internet network.
Internet Architecture and Data Routing
The shaping of cyberspace by both Russia and Ukraine is based on the technical principles of data routing. As per the International Telecommunication Union (ITU), the Internet is “a collection of interconnected networks using the Internet Protocol which allows them to function as a single, large virtual network”.
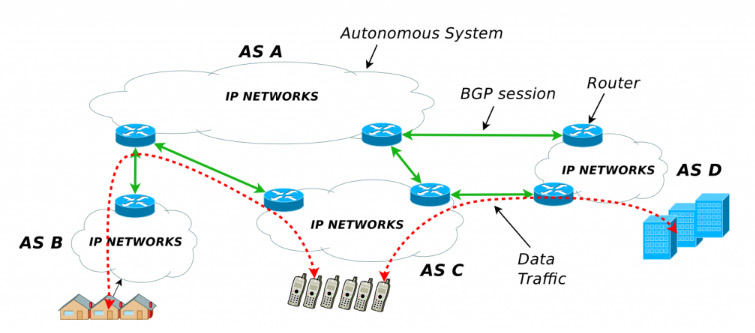
As shown in Figure 1, these interconnected networks are called Autonomous Systems (ASes). An Autonomous System (AS) itself is a network that manages the internal routing of data, distributes Internet Protocol (IP) addresses, and sets standards for access policies. Data or Internet routing is the assignment of a path for the data package through which this package reaches its destination. Currently, data routing happens through a routing protocol called Border Gateway Protocol (BGP), which is used in inter-domain routing for ASes. A Regional Internet Registry (RIR) allocates Autonomous System Numbers (ASN) to its ASes and IP addresses to the users within the ASes. An AS establishes a BGP exchange-of-data session with other ASes. These BGP sessions are Transmission Control Protocol (TCP) sessions between two routers connecting different ASes. TCP is essential to manage and keep the connections open.
Autonomous Systems are Internet Service Providers that can be controlled by governments, universities, or companies. Each AS has an administrator that communicates and agrees to a path followed by data packets to other ASes which is made possible through a BGP. In the initial stages of the growth of the internet, the protocol for routing followed a more decentralised structure. Any system on the network was a possible gateway. However, as the networks became more complex, there was a visible hierarchy between paths taken by the data packets and some transit points became more important than others based on commercial, political, and geographical reasons. Geopolitical reasons can impact the number of gateways a region has. For example, a remote island like Tonga is connected to the world only through one submarine cable via Fiji, hence, limiting its number of gateway entries severely. China’s Great Firewall, Iran’s Halal Internet, and Russia’s Sovereign Internet are all based on the efforts of these states to better control data and content flow through a combination of techniques including IP blocking, DNS tampering and hijacking, and deep packet inspection and keyword filtering.
Who governs the internet?
The absence of a central organisation to oversee internet operations does not imply that everyone can have unrestricted access. For example, IP addresses and hostnames are finite and are bound by technical and geographical restrictions. The delegation of hostnames and IP addresses was controlled by the United States (US) until 2009, when the US government gave autonomy to ICANN to operate independently. The US Department of Commerce still played a role in reviewing the operations of ICANN till 2016. Another entity called the Internet Engineering Task Force (IETF) consists of experts that develop and approve protocols needed for Internet functioning and is considered to be free of political interference, unlike ICANN. Nonetheless, ICANN does not have the authority to debar any actor from the Internet.
Amidst the Russia–Ukraine conflict, the Ukraine Government sent a request to ICANN’s Government Advisory Committee for revoking the Russian Internet country code ‘.ru’ and its Cyrillic equivalence but this request was rejected. This rejection notwithstanding, it is within the capabilities of ICANN and the Europe and Central Asia’s Regional Internet Registry to take back all IP addresses assigned to Russia, essentially causing Russian websites to disappear from the Internet.
Russia–Ukraine Internet Infrastructure
In December 2019, Russia successfully conducted a test of disconnecting its network from the global internet as an attempt to ‘test its cyber defences’. This test was based on the Sovereign Internet/RuNet law passed by the Russian Government in November 2019. The law is implemented and monitored by Roskomnadzor, a Russian federal communications agency. Under the law, it is mandatory to install certain tracking software and hardware at all internet gateway points across Russia.
The Russian government has stated that the legislation is in response to the US’s 2018 National Cybersecurity strategy that aims to ‘build a more lethal joint force’ and ‘compete and deter in cyberspace’. While Russian analysts justify their country’s concern vis-à-vis US big tech companies’ influence, the flipside is that the Russian government now has complete control over what its citizens consume online. Also, Russian fear of the US cutting it out from the global internet is not in-sync with her accusation of the US using its big tech companies’ platforms to influence Russian citizens. This is because it would have been in American interest to keep Russians connected to the global Internet to influence them. Russia’s Sovereign Internet law is based on politics surrounding data routing which has led to further fragmentation of the Internet in the region.
On the Ukrainian side, its Internet architecture is split between the two global powers—the US, with a few European ASes and Russia. It is connected to Russia through 95 ASes (comprising Rostelecom, Rascom, and Transtelecom) and to the US via ASes, mainly through the Hurricane Electric AS. Ukraine’s connections with Russia have fallen sharply since the 2014 Russo-Ukrainian conflict. From 2019 onwards, the US has increased its AS connections with Ukraine mainly due to Russia’s attempts to control the data flow in Eastern Ukraine, especially in the Donbas region.

Russian Virtual Control in Crimea and Donbas
In the 2014 Russo-Ukrainian conflict, the regions of Crimea and Donbas, situated broadly on the eastern and southern sides of Ukraine, were vociferously fought over by Russia and Ukraine. Following this, Crimea came under Russian control and the territories of Donetsk and Luhansk in Donbas came under the authority of Russian-backed separatist groups. Russia also has control over the region’s water and energy supply, internet access, and crucial infrastructure. By 2018, Russia had succeeded in the complete integration of Crimean and Donbas’ network with the Russian network.
Before Russia’s successful integration of Crimea’s economic, bureaucratic, infrastructural, and informational apparatus, Crimea’s network adhered to Ukrainian rules and regulations. Post-annexation, Crimea’s Internet infrastructure is entirely integrated with the Russian network. The integration started with the Russian-backed Crimean government building the necessary infrastructure to replace the Ukrainian network.
Secondly, Russia attempted to truncate all direct links between Crimea and Ukraine. Ukrainian actions did not help its case as it put sanctions against ASes (Russian included) operating in Crimea post-annexation. This further diminished Ukrainian control and access to the region and resulted in the creation of small Crimean ASes connected to Russia-registered ASes like Miranda Media, Crelcom, and CrimeaCom.
Finally, Russia aggressively started building telecommunications infrastructure to connect with Crimea. Russia’s state-owned telecom company Rostelecom built a 110 Gbps submarine link called the Kerch Strait Cable from Russia to Crimea, costing $25 million. Therefore, from 2014 to 2017, Russia gradually altered Crimea’s internet routing routes, essentially moving data through Russia. By mid-2017, no more data paths from Crimea were going through Ukrainian ASes. This signifies that Russia-influenced ASes started operating in Crimea, establishing their BGP agreements, and ousting the Ukrainian network. As a result, since 2014, Crimeans have been watching on the internet what Russians want them to see. For the Russian Federation, the lessons they learned from the Crimean experiment were significant and they wasted no time in applying the same strategy to Donbas.
Donbas
Where Eastern Ukraine differs from Crimea is the ambiguous political nature of its relationship with Russia and Ukraine, with neither country having complete control over the region. Russia’s attempt to control internet routing has been challenging because its network is far more complex with many more actors operating in the region than in Crimea. Reports note that even though there are several direct links between Russia and Ukraine, since 2014, the data flow between these routes has severely dropped. The level of Russian control over Donbas is hard to access but according to research by the University of Paris, there are no data routes between Donbas and Ukraine anymore. Further, a data package from Donbas directly reached Russia without any rerouting. What this essentially means for Donbas locals is that they have slower connectivity for higher prices and complete Russian control on what they are allowed to access online. Furthermore, the Donbas network is now part of the Russian Sovereign Internet/RuNet indicating the possibility of online surveillance, data capture, and censorship. Hence, Russian control over the Donbas network indicates its intention to bring the entire Donbas territory under its influence/ authority.
Is RuNet a Failure?
The Russia–Ukraine conflict, as well as Russia’s 2014 annexation of Crimea, draw light on the geopolitics of data routing and the usage of the Border Gateway Protocol (BGP) as a tool of control. BGP is used by states to monitor and ensure censorship, block users and websites, carry out cyberattacks on other internet infrastructures, and hijack traffic from other networks. Russia not only successfully created a Sovereign Internet named RuNet, out of concerns that the West can constrict its access to global internet and to ostensibly protect its citizens from alleged disinformation and cyberattacks, but has also integrated the Donbas and Crimean networks into RuNet. Has the current conflict between Russia and Ukraine reaffirmed the Russian campaign for Sovereign Internet?
Firstly, Russia established RuNet to ensure protection from cyberattacks. Russia’s Foreign Ministry alleged that the US and its allies have put together a group of internal “offensive cyber-forces”, attacking Russia’s critical infrastructure. Therefore, RuNet, it seems, has not been successful in stopping cyberattacks. Secondly, as a result of Russia’s military operation in Ukraine, Western big tech companies and their platforms have pulled out of the country. This, of course, does not equate to Russia being barred from the global internet. ICANN and the US have repeatedly stated that the Russian Internet will not be blocked. Therefore, Russian concern of being blocked from the global internet by the West has not materialised. Thirdly, Russian backing of RuNet to protect its citizens from alleged Western disinformation too has not been successful. Reports note that Russians are finding several technical workarounds to bypass the RuNet. Finally, the creation of such splinternets, have made the business of data routing slower and more expensive in Donbas and Crimea, forcing the local governments there to unnecessarily invest in infrastructure for connectivity with Russia. It would seem that Russia has not been able to fully achieve the objectives which led the country to develop RuNet.
Krutika Patil, Research Assistant for the Project on Cyber Security at the Institute for Defence Studies and Analyses, New Delhi
Views expressed are of the author and do not necessarily reflect the views of the Manohar Parrrikar IDSA or of the Government of India.
This is the abridged version of the article which appeared first in the Comment section of the website (www.idsa.in) of Manohar Parrikar Institute for Defense Studies and Analyses, New Delhi on May 4, 2022